Tor - The Onion Router Square Sticker | Zazzle.com in 2021 | Router, Custom stickers, Create custom stickers
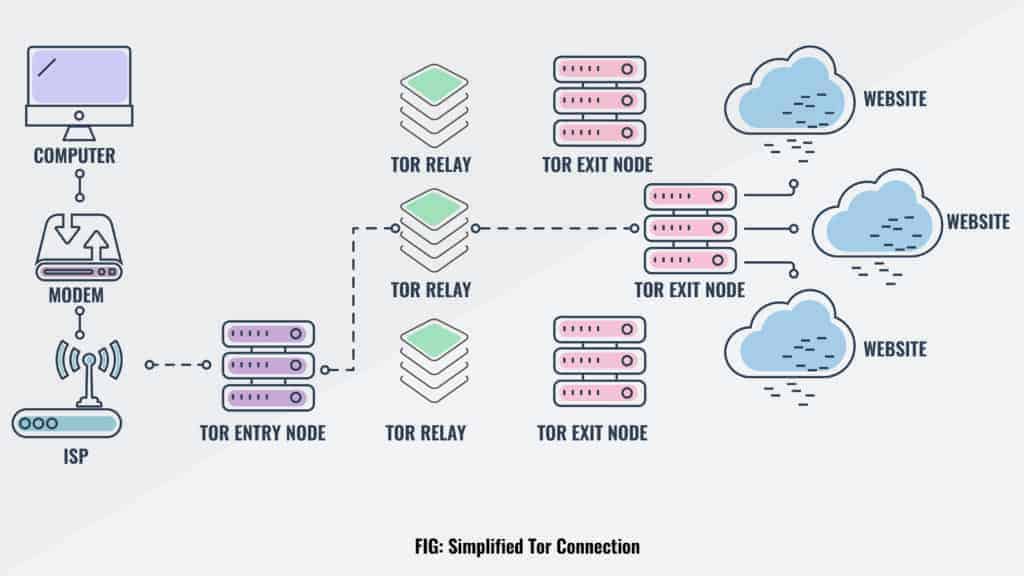
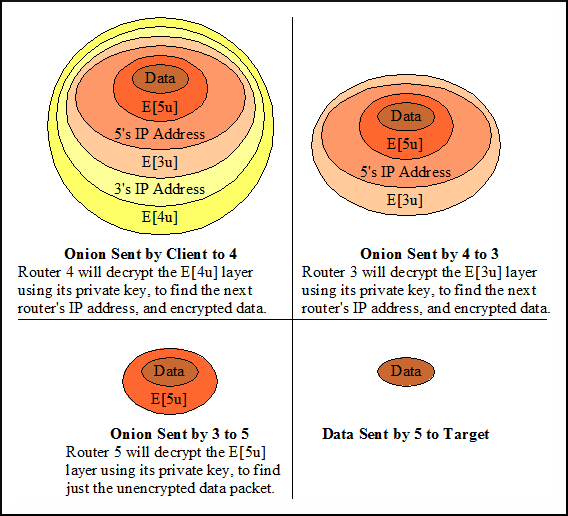
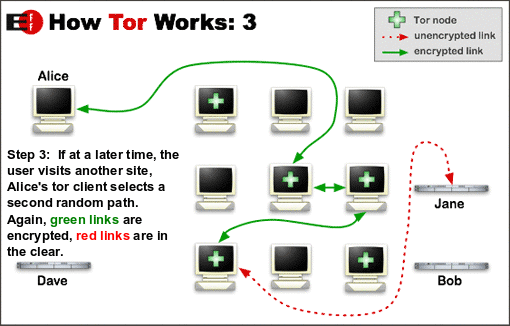
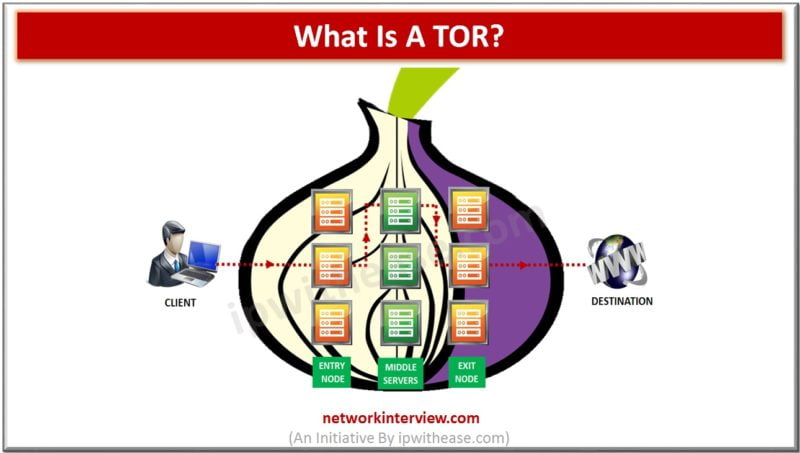
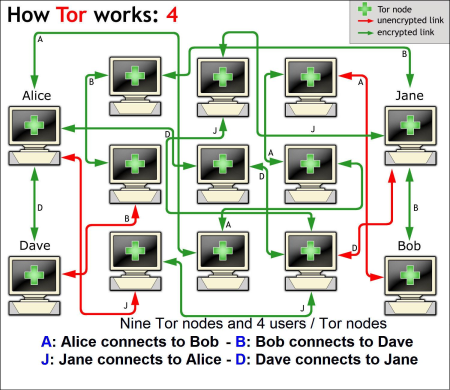
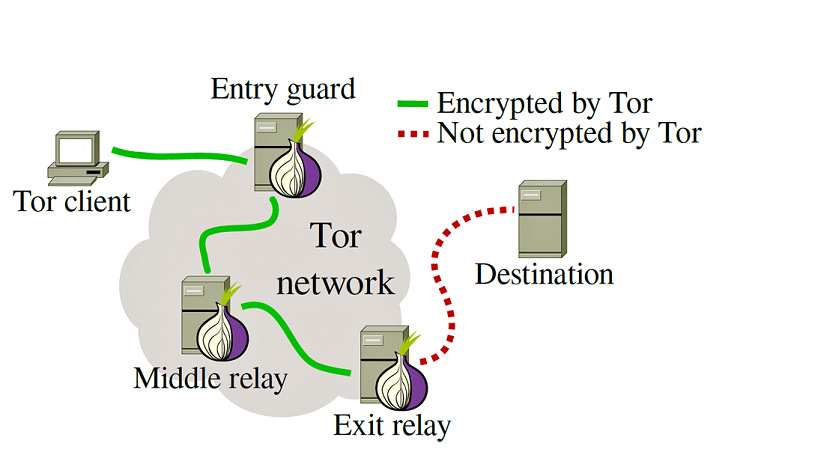
Understanding the Tor Network. The Onion Router, Tor, is a free… | by Amanda_James_Min | Systems and Network Security | Medium

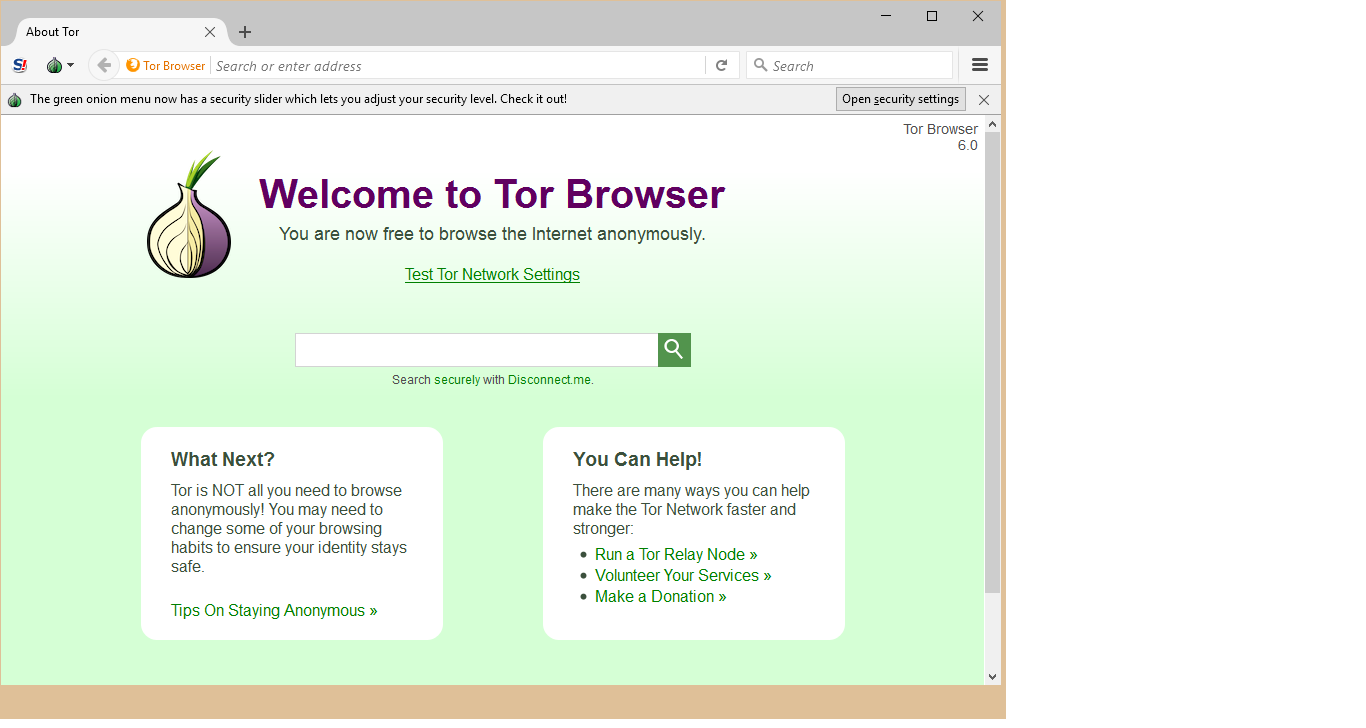
Tor or the Onion Router Website Homepage. Editorial Stock Photo - Illustration of client, onion: 131264938